PHPki
Maintainer
Previous: [1]Daniel B. from Firewall Services
Now maintained by Koozali SME
Version
Old version prior SME10:smeserver-phpki and phpki
New Version:
Please follow the installation instructions below. The installation instructions will satisfy all dependencies and the latest versions of the above 2 RPMs will be installed automatically.
Description
PHPki is an Open Source Web application for managing a multi-agency PKI for HIPAA compliance. With it, you may create and centrally manage X.509 certificates for use with S/MIME enabled e-mail clients, SSL servers, and VPN applications. PHPki is now used to manage certificates with the latest release of the SME Server OpenVPN Bridge contrib.
You can see a demo installation here.
Requirements
Installation
- install the rpms
yum --enablerepo=smecontribs install smeserver-phpki-ng
go to the server-manager to the manage certificate menu and start creating your CA certificate
Warning click only once and wait for the page to update it can be very long to create the 4096 certificate...
you have to enable the epel repository
- install the rpms
yum --enablerepo=smecontribs,epel install smeserver-phpki
- and start/restart needed services:
expand-template /etc/httpd/conf/httpd.conf expand-template /etc/httpd/pki-conf/httpd.conf sv t /service/httpd-e-smith sv u /service/httpd-pki
- alternatively issue the following :
signal-event post-upgrade; signal-event reboot
on update you can issue
expand-template /etc/httpd/conf/httpd.conf expand-template /etc/httpd/pki-conf/httpd.conf sv t /service/httpd-e-smith sv t /service/httpd-pki
For sme8
- install the rpms
yum --enablerepo=smecontribs install smeserver-phpki
- and start/restart needed services:
expand-template /etc/httpd/conf/httpd.conf expand-template /etc/httpd/pki-conf/httpd.conf sv t /service/httpd-e-smith sv u /service/httpd-pki
- alternatively issue the following :
signal-event post-upgrade; signal-event reboot
Configure your new PKI
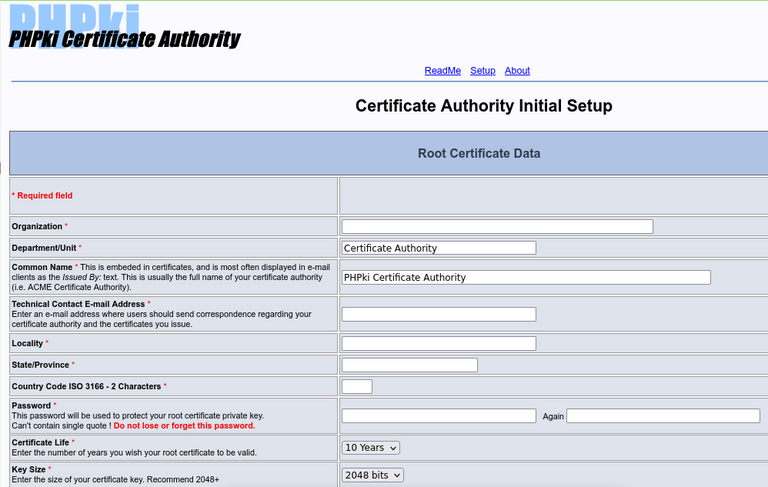
Go in the server-manager, you'll find a new "Manage Certificates" menu (or you can use the URL https://server.domain.tld/phpki/ca) Here you have to enter the following informations:
- Organisation
- Department
- Common Name of the Master CA
- E-mail (technical contact)
- City
- State
- Country Code
- Password (to protect the private key of the Master CA)
- Validity of the CA
- Keys size
- URL of your PKI (https://my.domain.tld/phpki)
These two screenshots illustrate the first (and the most important) part of this configuration page:
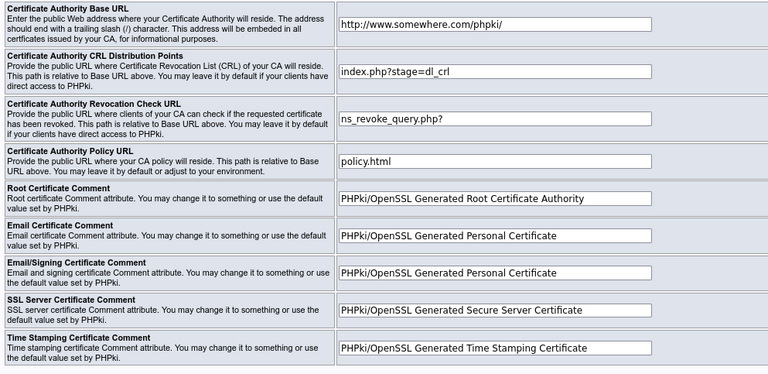
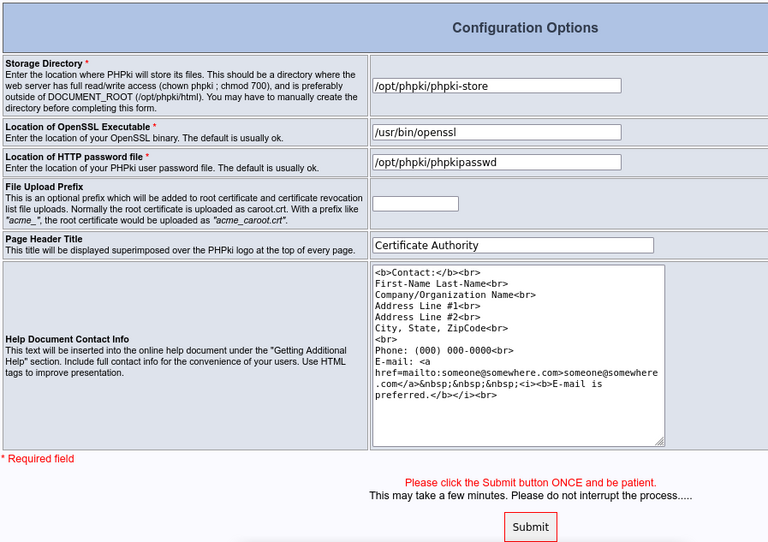
The second part is like this:
The default settings should be OK for most installations. You may just want to change the "Help Document Contact Info" part.
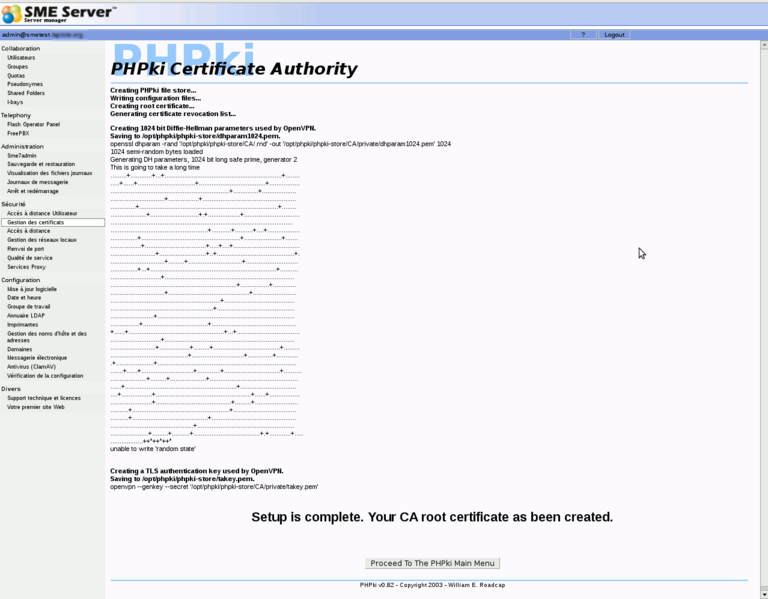
Once you have submitted this form (which can take several minutes, be patient, as generating dh parameters can take a long time), you should have something like this:
Now you'll be able to start using PHPki. It's quite easy to use.
The administrative interface is available on the server-manager or directly https://my.domain.tld/phpki/ca
There's also a public interface, available only from the local networks, but without password at https://my.domain.tld/phpki. Here, users can download the Master CA certificate, the CRL, or search for certificates of other users (public part only of course).
Add another admin
if you happen to need to delegate certificate generation, you can use user-panel to add access to the panel, but you will also need to add the user manually to phpki config
edit /opt/phpki/phpki-store/config/config.php
#$PHPki_admins = Array(md5('admin'));
$PHPki_admins = Array(md5('admin'),md5('user2'));
Uninstall
To uninstall the contrib from your server, just run the following commands:
yum remove smeserver-phpki-ng phpki-ng expand-template /etc/httpd/conf/httpd.conf systemctl restart /service/httpd-e-smith
Certificates and PKI configuration are stored in /opt/phpki/phpki-store, php files are in /opt/phpki/html
Re-install
before phpki-ng 0.84-14
If you have removed the contrib, and want to re-install it keeping your previous CA (assuming you restored /opt/phpki), you'll need to follow these steps after you have installed the rpms:
cd /opt/phpki/html/ rm -f index.php rm -f setup.php ln -s main.php index.php cat config.php.rpmsave > config.php cd ca rm -f index.php ln -s main.php index.php cd /opt/phpki/ chown phpki:phpki -R phpki-store chown root:phpki -R html/config.php
Bugs
Please raise bugs under the SME-Contribs section in bugzilla.
smeserver-phpki-ng
For the new smeserver-phpki-ng, select the smeserver-phpki-ng component or use this link
| ID | Product | Version | Status | Summary (4 tasks) ⇒ |
|---|---|---|---|---|
| 12436 | SME Contribs | 10.0 | CONFIRMED | failure to download crl |
| 12426 | SME Contribs | 10.0 | CONFIRMED | smeserver-phpki-ng Setting httpd-pki PHPVersion does not alter template |
| 12228 | SME Contribs | 10.0 | RESOLVED | wrong uid and gid |
| 10903 | SME Contribs | Futur | CONFIRMED | NFR: Save certificate bundle for ovpn configs |
phpki-ng
For the new phpki-ng itself select the phpki-ng component or use this link
| ID | Product | Version | Status | Summary (2 tasks) ⇒ |
|---|---|---|---|---|
| 12420 | SME Contribs | 10.0 | CONFIRMED | phpki-ng Create and download file has no name |
| 12275 | SME Contribs | 10.0 | CONFIRMED | PHP Warning: Use of undefined constant |
Changelog
Only released version in smecontrib are listed here.
- fix httpd needs QSD in place of ? [SME: 12354]
2022/12/28 Jean-Philippe Pialasse 0.3-21.sme
- fix chop isntead of chomp for config.php [SME: 12293]
- small fixes for config.php and httpd
2022/12/14 Jean-Philippe Pialasse 0.3-18.sme
- revert log/phpki [SME: 12266]
- phpki-ng autopopulate base info from ldap [SME: 11440]
- ensure user are seen by php-pool [SME: 12268]
- safe remote access for crl [SME: 11439]
- fix typo preventing httpd-pki to start 2
- add dl_crl_pem.php [SME: 12272]
- fix regex and potential code injection [SME: 12274]
2022/12/14 Jean-Philippe Pialasse 0.84-14.sme
- add easy and safe access to crl download [SME: 12272]
- fix revoke certificate failing on whitespace pass [SME: 12273]
- fix missing default_md in config.php from previous versions [SME: 12267]
- remove extra space in URL in search.php [SME: 12232]
- Attempt to fix the final reload after CA creation [SME: 11192]